Embracing the Future of Access Control: Physical vs. Mobile Card Credentials
In the evolving landscape of security and access control, organizations are constantly seeking more efficient, secure, and convenient ways to manage entry into their premises. As technology advances, the shift from traditional physical card access credentials to mobile card access credentials is becoming increasingly prevalent. This transition is not just a matter of swapping one medium for another; it represents a significant leap forward in how access control systems are designed, managed, and experienced. In this context, the role of a seasoned security integrator like Systems Integrations becomes crucial in facilitating a smooth migration to mobile credentials. Let’s delve into the pros and cons of each type of access credential and explore how Systems Integrations can guide organizations through this transition.
Physical Card Access Credentials
Pros:
- Widely Adopted: Physical access cards are a well-established standard in access control systems across various industries, making them a familiar option for both users and security personnel.
- Simplicity: They offer a straightforward, no-frills approach to access control. Users simply swipe or present their card to gain entry, requiring minimal instruction or training.
- Compatibility: Physical cards are compatible with a wide range of existing access control systems, allowing for easy integration with other security measures.
Cons:
- Loss and Duplication: Physical cards can be easily lost, stolen, or duplicated, posing a significant security risk. Reissuing lost cards incurs additional costs and administrative overhead.
- Environmental Impact: The production and disposal of plastic access cards contribute to environmental waste, a growing concern for many organizations.
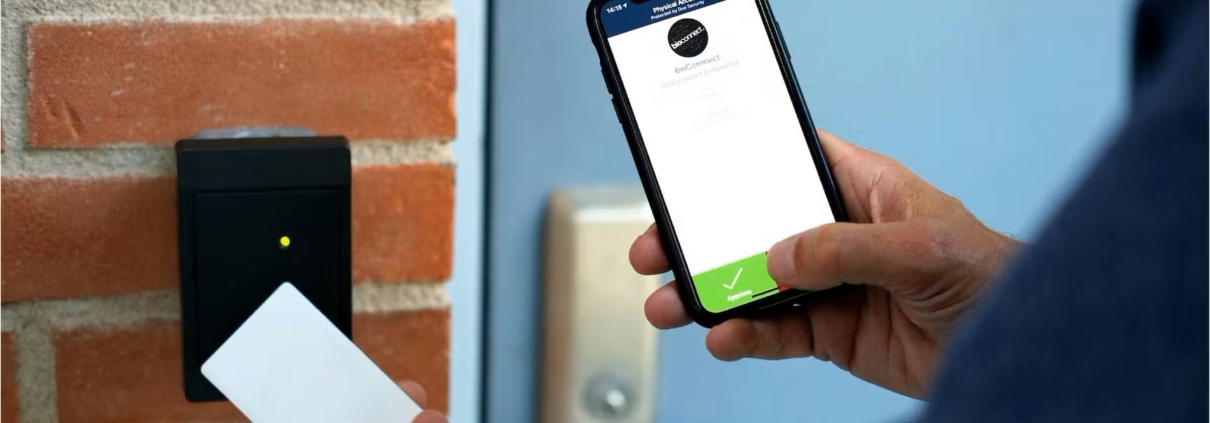
Mobile Card Access Credentials
Pros:
- Enhanced Security: Mobile credentials leverage encryption and dynamic data exchange, making them significantly more secure against cloning or unauthorized access than traditional cards.
- Convenience and Flexibility: With mobile credentials, smartphones become the access tool, eliminating the need for carrying separate access cards.
- Cost-Effective and Eco-Friendly: Transitioning to mobile access eliminates the need for physical card production and management, reducing costs and environmental impact over time.
Cons:
- Dependency on Smart Devices: Mobile credentials require users to have a compatible smartphone or device, which may not be feasible for everyone.
- Technology Adaptation: Some users or organizations may resist the change due to unfamiliarity with technology or the need for new infrastructure to support mobile access.
- Security Concerns: While inherently secure, mobile credentials depend on the security of the user’s device. Compromised or lost devices pose a potential security risk.
How Systems Integrations Can Facilitate the Transition
Systems Integrations plays a pivotal role in navigating the complexities of migrating to mobile credentials. With expertise in the latest security technologies, Systems Integrations can:
- Assess Needs and Infrastructure: Begin with a comprehensive assessment of the current access control system and identify the most effective migration path to mobile credentials.
- Custom Solution Design: Design a tailored solution that integrates seamlessly with existing security systems while leveraging the advantages of mobile technology.
- Implementation and Training: Oversee the implementation process, ensuring minimal disruption. Provide thorough training for staff and users to ensure a smooth transition.
- Ongoing Support and Upgrades: Offer continuous support and system upgrades to enhance security and functionality, adapting to emerging threats and technological advancements.
The shift from physical to mobile card access credentials offers a compelling array of benefits, including enhanced security, convenience, and environmental sustainability. However, the transition requires careful planning, execution, and support to address potential challenges and ensure a seamless integration. With the expertise of a security integrator like Systems Integrations, organizations can confidently navigate this transition, unlocking a new era of access control that aligns with the demands of the modern world.